Two years after Microsoft introduced its first wave of ‘Copilot+’ Windows PCs, designed to leverage neural processing units (NPUs) for enhanced AI and machine learning capabilities, the Recall feature has come under scrutiny. Initially intended to track user activity through screenshots for memory recall, Recall's implementation raised significant privacy concerns. Reports highlighted that it stored user data in unencrypted files, making sensitive information easily accessible to anyone with local or remote access.
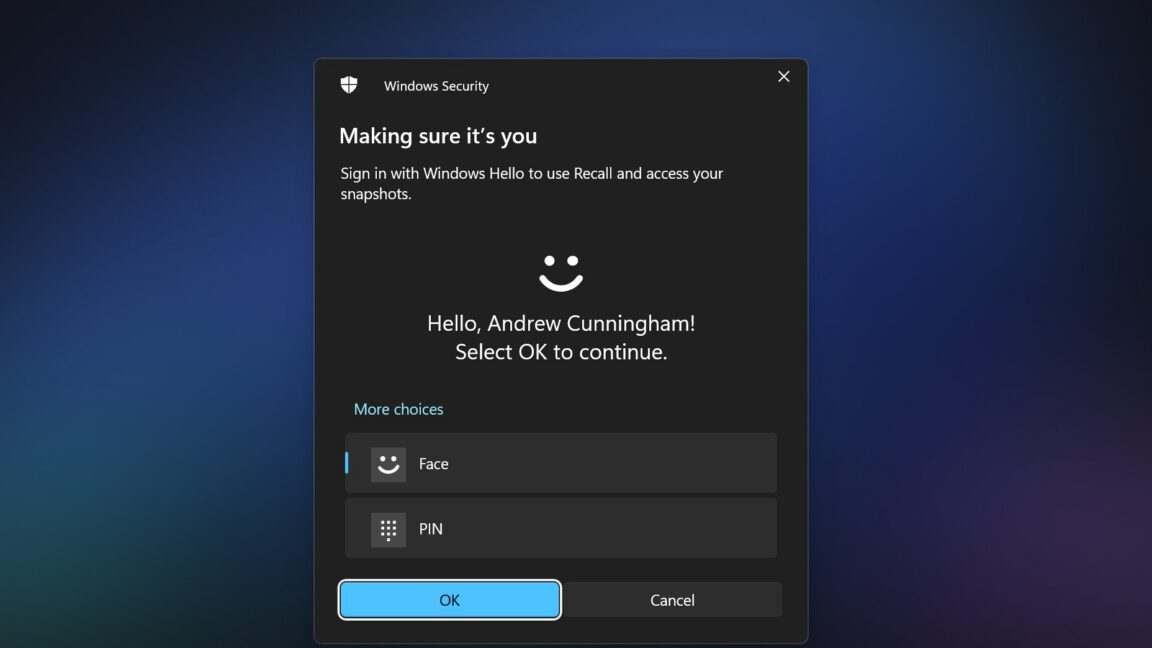
In response to these security lapses, Microsoft delayed the Recall rollout by nearly a year, subsequently enhancing its security measures. The new version of Recall encrypts locally stored data, restricts access to authenticated users via Windows Hello, and aims to filter out sensitive information like financial data. Furthermore, Recall is now disabled by default on PCs that support it.
Despite these improvements, security researcher Alexander Hagenah, who previously developed the original TotalRecall tool, has introduced an updated version called TotalRecall Reloaded. This tool is designed to exploit potential vulnerabilities in the Recall feature, focusing specifically on the security around the AIXHost.exe process, which handles data sent from Recall after user authentication.
According to Hagenah, while the security surrounding the Recall database is robust, the AIXHost.exe process lacks the same protective measures. He described the situation metaphorically: “The vault is solid; the delivery truck is not.” The TotalRecall Reloaded tool works by injecting a DLL file into AIXHost.exe, allowing it to intercept screenshots, OCR text, and metadata transmitted to this process. This interception can occur even after the user has ended their Recall session.
Understanding the Risks
Hagenah's analysis indicates that while the VBS enclave within the system does not decrypt data without Windows Hello authentication, the TotalRecall Reloaded tool does not bypass this requirement. Instead, it operates alongside the user’s authentication process, waiting for the moment the user provides access. There are also specific actions, such as retrieving the most recent Recall screenshot or deleting the entire Recall database, that can be performed without requiring Windows Hello authentication.
Once authenticated, the tool can access both new data recorded in Recall and previously stored information. This raises significant privacy concerns, as anyone with access to a user's PC and their Windows Hello fallback PIN could potentially exploit this vulnerability.
Microsoft responded to Hagenah's findings, asserting that the issue he reported does not constitute a bug and does not warrant a fix. After investigating the access patterns, Microsoft classified the situation as consistent with their intended protections. A spokesperson stated, “The authorization period has a timeout and anti-hammering protection that limit the impact of malicious queries.”
Ongoing Privacy Concerns
Regardless of Microsoft's assurances about the security of Recall, the feature still poses a considerable risk to user privacy. Users must be aware that if someone gains access to their PC and their Windows Hello fallback PIN, they could potentially access a wealth of sensitive information, including emails, messages, and web activity. While Recall's content filters attempt to exclude sensitive financial information, they may not adequately protect against other types of personal data.
The scope of information that Recall can capture has prompted various app developers to implement measures to safeguard user privacy. For example, the Signal Messenger app on Windows has adopted a default setting that forces Recall to ignore its content, employing a flag typically used to protect DRM content. Other applications, such as the AdGuard ad blocker and the Brave browser, have implemented similar strategies to mitigate risks associated with the Recall feature.
In conclusion, while Microsoft has made strides in improving the security of the Recall feature in Windows 11, the revelations surrounding the TotalRecall Reloaded tool highlight ongoing vulnerabilities that users should remain vigilant about. The balance between convenience and privacy remains a critical concern as technology continues to evolve.
Source: Ars Technica News
